
Cyber insurance
Cyber insurance
Cyber insurance, also called cybersecurity insurance, protects small businesses from the high costs of a data breach or malicious software attack. It covers expenses such as customer notification, credit monitoring, legal fees, and fines.
What is cyber insurance and why is it important for small businesses?
Cyber insurance helps businesses recover from data breaches and cyberattacks, which are increasingly common and costly. It provides crucial protection for businesses that handle sensitive information that could be exposed in a security breach.
A data breach isn't just an inconvenience—it can put you out of business. The average cost of a breach is $10.22 million in the United States. Nearly 43% of cyberattacks are against small businesses, which are targeted due to their vulnerabilities, such as less investment in cybersecurity.
Cyberattacks and data breaches can incur a wide range of expenses, such as customer notifications, credit monitoring, attorney's fees, fines, data recovery, and forensic investigations. A cyber insurance policy would cover all of these costs.

Businesses that purchase cyber insurance typically handle:
- Customer names, email addresses, phone numbers, and street addresses
- Credit card or bank account information
- Protected health information (PHI)
- Social Security numbers or driver's license numbers
- Cybersecurity for other businesses
What does cyber insurance cover?
Cybersecurity insurance covers your incident response costs associated with data breaches and cyberattacks, including the cost of recovering important data and hiring legal representation.
There are two types of cyber insurance coverage: first-party coverage and third-party coverage.
Most businesses need first-party cyber coverage to defend against their own cyber risks, especially if they handle personally identifiable information (PII) for customers.
Companies that are responsible for their clients' cybersecurity would need third-party cyber liability insurance to provide legal protection from client lawsuits.
What is first-party cyber insurance?
First-party cyber insurance coverage, sometimes called data breach insurance, covers costs related to a data breach or cyberattack that directly impacts your business.
Small business owners can often add this coverage to their general liability insurance. It’s recommended for businesses that collect personal information, such as customer email addresses or credit card numbers.
Specifically, first-party cyber insurance can help cover:
Data breach response costs
State laws typically require a response when a business is impacted by a data breach. Cyber insurance helps cover costs associated with hiring a digital forensic expert to investigate the breach, customer notifications, consumer credit and fraud monitoring services, as well as Payment Card Industry (PCI) compliance fines.
Business interruption expenses
When a cyber incident brings necessary systems offline or otherwise grinds business to a halt, cyber insurance can help cover business interruption expenses, such as lost income and the cost of hiring additional staff or renting equipment. This includes purchasing third-party services, such as hiring a public relations manager or crisis management team.
Ransomware payments
If a hacker encrypts private information about your company or its employees and holds it for ransom, cyber insurance will help with payments to meet cyber extortion demands.
What is third-party cyber insurance coverage?
Third-party cyber insurance coverage helps pay for legal costs when a client sues your company for failing to prevent a data breach or cyberattack at their company. This insurance is recommended for tech companies that make software recommendations to clients or are responsible for their cybersecurity.
Third-party coverage can be bundled with your errors and omissions policy into what is known as technology errors and omissions insurance, or tech E&O.
Specifically, third-party cyber insurance can help cover:
Legal defense costs
If a client sues your business for failing to prevent a data breach at their business, tech E&O would help cover attorney's fees and other legal costs for your defense in court.
Settlements
If your business faces a lawsuit from a client who experienced a data breach, you and the client could decide upon a settlement out of court that would amend the damages they experienced.
Court-ordered judgments
If a client accuses you of being responsible for a data breach at their business and sues your company, you may be legally obligated to pay for damages from any judgments in the lawsuit.
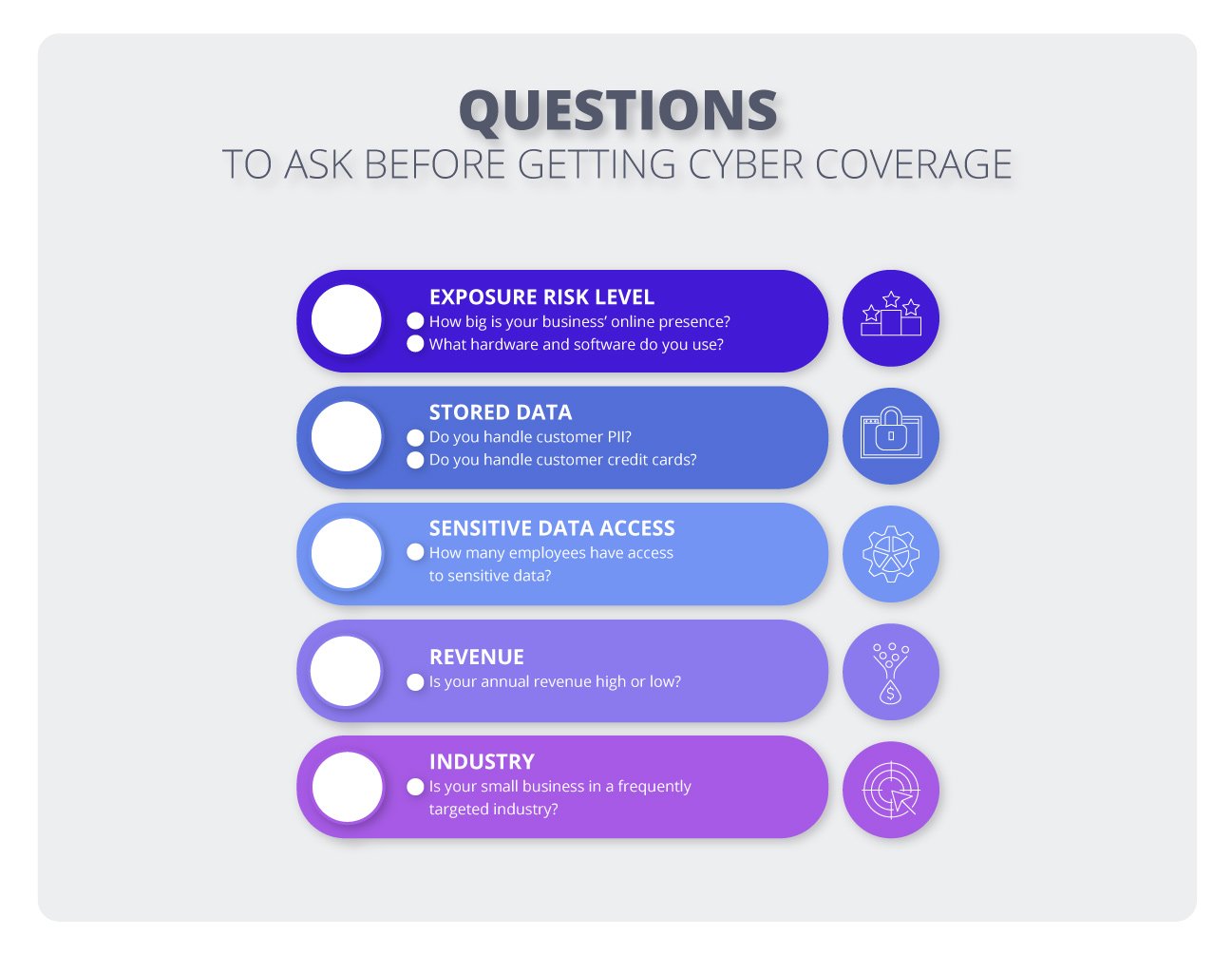
How much does cyber insurance cost?

Insureon customers pay an average premium of $134 per month for cyber insurance. The cost of cyber insurance is based on several factors, including:
- Your industry
- Amount of sensitive data handled
- Number of employees
- Cybersecurity controls at your business
- Policy limits and deductible
All of these factors will be instrumental in determining how much cyber insurance your small business needs.
Verified business insurance reviews
Hear from customers like you who purchased small business insurance.
Who needs cyber insurance?
Cyber liability insurance is a key policy for companies that operate in cybersecurity, work in a cloud environment, or handle sensitive customer information.
While any business can fall victim to a data breach or cyberattack, a few industries are particularly vulnerable, including:
IT professionals
Cyber insurance covers legal costs when a client blames your tech company for failing to prevent a data breach or cyberattack at their business.
For example, if an IT consultant leaves data for a small healthcare company unsecured on Amazon Web Services, and a cyberattack exposes hundreds of Social Security numbers and email addresses belonging to the company's customers, the healthcare company could blame the consultant and file a lawsuit.
The consultant's cyber liability policy would pay for legal defense costs and the eventual settlement.
Retail businesses
Cyber insurance helps retailers recover after a data breach or cyberattack on their business. It's recommended for any shop that handles customer email addresses, credit card numbers, or other personal information.
For example, an employee at your clothing store accidentally clicks on a link in a social engineering email containing a malicious computer virus. The virus encrypts data crucial to your business’s operations and demands a ransom for its retrieval.
Your cybersecurity insurance would reimburse you for the ransom and for the cost of hiring someone to look into the source of the attack. Cybercriminals commonly use social engineering to deceive employees into initiating these types of attacks.
Healthcare organizations
Healthcare organizations and medical service providers often have to abide by strict privacy and security guidelines, such as the Health Insurance Portability and Accountability Act (HIPAA), to avoid regulatory fines and other legal consequences.
Cyber insurance for medical practices can help cover financial losses and provide essential resources. That includes the cost of notifying clients that their data was exposed, credit monitoring services for affected clients, and PR campaigns to restore reputation.
For example, a denial of service (DoS) attack on a doctor's office disrupts their appointment scheduling system and other online services. The consequences include lost profits, reputational damage, and difficulties obtaining patient care.
Cyber insurance would cover business interruption expenses while the facility works to reboot and upgrade security on its system. It would also help pay for a PR campaign and any related fines or legal fees.
Financial service providers
Cyber insurance can cover legal fees and expenses for financial professionals, while also providing vital resources to help with recovery efforts if they experience a cyberattack or data breach.
For example, if a tax preparer asks a client to upload a document with sensitive data online and that client data is stolen or compromised, the affected client might decide to sue the tax preparer to recoup expenses.
Cyber liability insurance can shield your business from legal expenses related to a data breach by paying for court costs and attorney fees.
Real estate professionals
Cyber insurance for real estate professionals can help pay for recovery expenses while also providing resources to help aid customers affected by data breaches and other cyber risks.
For example, a real estate agent loses a laptop containing sensitive client information. The data breach laws in their state require them to notify their customers, and they also run a PR campaign to help restore trust.
Cyber insurance would provide coverage for notification costs, PR efforts, fraud monitoring services, and other related expenses.

Network security and privacy liability insurance, also called cyber liability insurance, protects small businesses from the significant costs of data breaches and malicious software attacks. This coverage includes legal fees, penalties, and credit monitoring services.
How to protect your business from cyberattacks
WARNING! WARNING! WARNING! WARNING! WARNING!
Cyberattack! Cyberattack, oh yeah!! It's a cyberattack!
Don't worry, you have cyber liability insurance. Your small business is protected from cyberattacks and data breaches that can cost thousands of dollars.
Got it bad! Got it bad! Got it bad! Cyberattack!
What the heck, man? So, no encore? I'm gonna need a ride home. Can someone call my mom?
You can get all the coverage your business needs by following this link. Protection is peace of mind.
Data breaches are expensive and can take a long time to resolve. On average, it can take around 240 days for resolution if a breach is discovered internally, or closer to 320 days if the breach is disclosed by a hacker, according to a study by IBM and the Ponemon Institute. The study found that only one-third of breaches were discovered by an organization’s own staff.
A cyber insurance policy can help pay for:
- Mandatory notification of affected parties
- Investigating and fixing security flaws
- Credit monitoring services for affected customers
- Reputational harm and loss of business opportunities
Complete our easy online insurance application to get free cyber liability insurance quotes that meet the needs of your small business.
What does cyber liability insurance not cover?
While cyber insurance covers costs related to cyber threats, it does have a number of coverage exclusions. For example, it does not cover data loss caused by a power outage.
Other exclusions from cyber liability insurance coverage include:
Mistakes and oversights
Professional liability insurance, also called errors and omissions insurance, covers the costs of lawsuits related to professional negligence. That includes mistakes, oversights, missed deadlines, and other negligent acts that harm a client.
Damaged electronics
If you experience data loss during a power surge, fire, or natural disaster, you would need electronic data processing (EDP) insurance. You can typically bundle this coverage in a business owner's policy (BOP).
It provides protection for your electronic devices, such as laptops, smartphones, and backup systems, along with the data they contain.
Physical accidents that destroy client data
While a cyber insurance policy covers data lost in a cyberattack, it does not insure data lost from accidental physical damage to a computer or storage device. For instance, a computer repair technician might accidentally drop a customer's laptop while trying to fix it, destroying all the data.
Electronic data liability coverage expands the third-party liability coverage in your general liability insurance to include loss of data caused by accidental damage to a customer’s computer, hard drive, or other data storage device.
General liability insurance
Business owner’s policy
Workers’ compensation insurance
Commercial auto insurance
Commercial umbrella insurance

FAQs about cyber insurance
Get answers to common questions about cyber threats and cyber insurance.
How do data breaches happen?
Data breaches can happen for a variety of reasons. In 2025, most breaches (51%) were malicious or criminal attacks, while 26% were caused by human error and 23% by an IT failure.
Security breaches are more likely to happen when your software is out of date or when your business lacks cyber controls, such as firewalls and multi-factor authentication.
Employee training is also essential. An untrained employee might download malware, click on a link in a phishing email, or fail to install important updates.
When a data breach or cyberattack occurs at a business, cyber insurance helps pay for an incident investigation, data recovery, and other related costs. Learn more about protecting your business from ransomware attacks and other threats.
What are some examples of data breaches and cyberattacks?
Cybercrime is a multibillion-dollar industry. Security firms constantly struggle to stay ahead of hackers looking for lucrative victims. Even with careful security measures in place, catastrophic data breaches can, and do, occur.
Here are a few examples of recent data breaches:
- More than 64 million people who applied for jobs at McDonald’s had their personal information exposed because the AI chatbot used to screen applicants had an administrator password of "123456."
- A ransomware gang threatened to release personal data belonging to almost a thousand Coca-Cola employees if they weren't contacted for a deal. When the company failed to respond, the hackers released 1,104 sensitive files, including copies of passports and visas.
- Six months after a previous data breach at MailChimp, cybercriminals accessed data belonging to more than a hundred MailChimp accounts through a social engineering attack.
Phishing emails, ransomware, malware, lost thumb drives, network security issues, and weak passwords are just a few examples of the kinds of cyber risks that could lead to a serious incident.
Be aware that small and midsize businesses account for 82% of ransomware attacks. Cybercriminals try to extort companies that are lucrative enough to pay a hefty ransom, but also small enough to make hacking attempts easier, as well as keep media and law enforcement attention low during the fallout.
Where can I learn more about cyber liability insurance?
If you want to learn more about this policy, you can find additional information in our frequently asked questions about cyber insurance.
If you have any other questions or if you'd like help finding the right insurance products for your small business, ask an Insureon agent.


























